NAT and PAT
Â
NAT is a feature of a router that will translate IP addresses. When a packet comes in, it will be rewritten in order to forward it to a host that is not the IP destination. A router will keep track of this translation, and when the host sends a reply, it will translate back the other way.
Home users who talk about NAT are actually talking about PAT, or Port Address Translation. This is quite easy to remember: PAT translates ports, as the name implies, and likewise, NAT translates addresses. Sometimes PAT is also called Overloaded NAT. It doesn't really matter what you call it, just be careful about blanket "NAT can't" statements: they are likely incorrect.
Now that that's out of the way, let's clarify some terminology required for a NAT discussion. When we refer to the inside, we're talking about the internal network interface that receives egress traffic. This internal network may or may not be using private addresses — more on those in a minute. The outside refers to the external-facing network interface, the one that receives ingress traffic. In the real world, it is not the case that NAT is simply using a single outside IP; translating traffic into internal IPs and ports. That's what your Linksys router does.
The "inside" of a NAT configuration is not synonymous with "private" or RFC1918 addresses. The often-referred-to "non-routable" addresses are not un-routable. You may configure most any router to pass traffic for these private IP subnets. If you try and pass a packet to your ISP for any of these addresses, it will be dropped. This is what "non-routable" means: not routable on the Internet. You can and should mix RFC1918 addresses (for management interfaces) on your local internal network.
NAT is not used to simply share a single IP address. But when it is, in this strange configuration that's really called PAT, issues can arise. Say two geeks want to throw up an IPIP tunnel between their networks so they can avoid all the issues of firewall rules and state-keeping. If they both use the same IP subnet, they can't just join two networks together: They won't be able to broadcast for each other, so they will never communicate, right? It would seem that one side or the other would have to renumber their entire subnet, but there is a trick. Using a semi-complicated NAT and DNS setup, the hosts could actually communicate. This is another case of blanket "NAT is evil" statements actually having little reflection on reality. This issue does come up frequently when two companies merge and various branch offices need to communicate.
So why in the world would someone want to use one external IP and map it to one internal IP, as opposed to just translating the port? Policy. It's even likely that both sides will use real bona fide Internet IP addresses. Everyone understands that NAT (the naive definition) will keep track of state; it's the only way to make translations happen. What they may not realize is that stateful filtering is a powerful security mechanism.
Stateful filtering means that the router will keep track of a TCP connection. Remember: a TCP connection consists of four parts: the remote and local IP address, and the connected ports. Stateful filters verify that every packet into the network is part of an already established, pre-verified connection.
Imagine a B2B transaction that ships sensitive data across the Internet, even between continents. It's not feasible to lay fiber for this purpose, so the Internet has to be used. What to do? How would you secure this transaction, or set of transactions? It can be done with IPSEC, but also utilizing NAT at the same time. Each side will have a 1:1 (real) NAT router configured to only allow specific connections from specific hosts. This guarantees that from either network, only authorized hosts will be making a connection. This also guarantees that hosts on both sides have been minimally exposed, and very unlikely compromised, since nobody else can get into that network.
Once the session starts, packets are carefully inspected in and out of each NAT router. If something nefarious happens, and someone in-between is able to inject a forged packet into the stream, at least one side will notice. One of the NAT routers will be able to detect that a sequence number anomaly has occurred, and can immediately terminate all communication. When the TCP session completes with a FIN, the state is wiped clean.
In much the same way, home users take advantage of PAT to keep their less-than-secure machines from being completely taken over on a daily basis. When a connection attempt from the outside hits the external interface of a PAT device, it cannot be forwarded unless state already exists. State setup can only be done from the inside, when an egress attempt is made. If this version of NAT didn't exist on such a wide scale, the Internet would be a completely different place. Nobody would ever successfully install and patch a Windows computer prior to a compromise without some the minimal protection provided by PAT.
Clearly, NAT is useful in these cases. So why do people say that NAT is evil? They are likely referring to PAT, the bastard child of NAT. It's called "overloaded" for a reason.
IPv6 introduces the capability to have way more IP addresses than we really need. Does that mean that IPv6 will eliminate NAT? No. It also won't eliminate the usage of NAT everyone's familiar with: PAT. We all need somewhere to stow Windows boxes away from the myriad of uninitiated connection attempts that come from the Internet.
Key Terms To Understanding NAT and PAT:
NAT
Short for Network Address Translation, an Internet standard that enables a local-area network (LAN) to use one set of IP addresses for internal traffic and a second set of addresses for external traffic.
PAT
Short for port address translation, a type of network address translation. During PAT, each computer on LAN is translated to the same IP address, but with a different port number assignment.
NAT and NAT types
Network address translation (NAT) is the process of modifying IP address information in IP packet headers while in transit across a traffic routing device.
The simplest type of NAT provides a one-to-one translation of IP addresses. RFC 2663 refers to this type of NAT as basic NAT. It is often also referred to as one-to-one NAT. In this type of NAT only the IP addresses, IP header checksum and any higher level checksums that include the IP address need to be changed. The rest of the packet can be left untouched (at least for basic TCP/UDP functionality, some higher level protocols may need further translation). Basic NATs can be used when there is a requirement to interconnect two IP networks with incompatible addressing.
However it is common to hide an entire IP address space, usually consisting of private IP addresses, behind a single IP address (or in some cases a small group of IP addresses) in another (usually public) address space. To avoid ambiguity in the handling of returned packets, a one-to-many NAT must alter higher level information such as TCP/UDP ports in outgoing communications and must maintain a translation table so that return packets can be correctly translated back. RFC 2663 uses the term NAPT (network address and port translation) for this type of NAT. Other names include PAT (port address translation), IP masquerading, NAT Overload and many-to-one NAT. Since this is the most common type of NAT it is often referred to simply as NAT.
As described, the method enables communication through the router only when the conversation originates in the masqueraded network, since this establishes the translation tables. For example, a web browser in the masqueraded network can browse a website outside, but a web browser outside could not browse a web site in the masqueraded network. However, most NAT devices today allow the network administrator to configure translation table entries for permanent use. This feature is often referred to as "static NAT" or port forwarding and allows traffic originating in the "outside" network to reach designated hosts in the masqueraded network.
In the mid-1990s NAT became a popular tool for alleviating the consequences of IPv4 address exhaustion. It has become a common, indispensable feature in routers for home and small-office Internet connections. Most systems using NAT do so in order to enable multiple hosts on a private network to access the Internet using a single public IP address.
Network address translation has serious drawbacks on the quality of Internet connectivity and requires careful attention to the details of its implementation. In particular, all types of NAT break the originally envisioned model of IP end-to-end connectivity across the Internet and NAPT makes it difficult for systems behind a NAT to accept incoming communications. As a result, NAT traversal methods have been devised to alleviate the issues encountered.
NAT Types
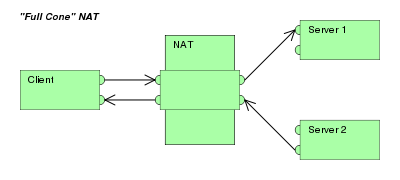
Full-cone NAT, also known as one-to-one NAT
|
|
(Address) restricted cone NAT
|
|
|
Port-restricted cone NAT
Like an address restricted cone NAT, but the restriction includes port numbers.
|
|
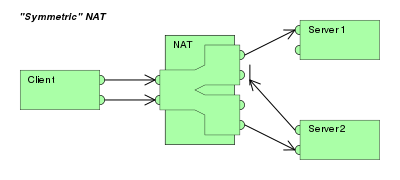
Symmetric NAT
|
NAT vs PAT difference
Network Address Translation (NAT) and Port Address Translation (PAT) both map IP addresses on an internal network to IP addresses on an external network. Which method of address translation you use depends on the types of networks that you are translating and the number of available IP addresses that you have.
If you are connecting a site in the 10.10.10.0 network to a site in the 10.10.20.0 network, you could use NAT to translate 10.10.10.0 IP addresses to available 10.10.20.0 IP addresses so that hosts on the 10.10.10.0 network can access data and use network resources on the 10.10.20.0 network. However, for this scenario to work, you must have an address pool that contains enough available IP addresses on the 10.10.20.0 network to accommodate every host on the 10.10.10.0 network, because NAT requires a one-to-one relationship when translating IP addresses.
PAT attempts to use the original source port number of the internal host to form a unique, registered IP address and port number combination. For example, two hosts that have been assigned the IP addresses 10.10.10.100 and 10.10.10.101, respectively, could send traffic to and receive traffic from the Internet by using the single public IP address 123.45.67.89. If that port number is already allocated, PAT searches for an available alternate source port number. Therefore, the host at IP address 10.10.10.100 could access the Internet by using the public IP address and source port combination of 123.45.67.89:10000. Meanwhile, the host at IP address 10.10.10.101 could access the Internet by using the IP address and source port combination of 123.45.67.89:10001.
If you are connecting a site in the 10.10.10.0 network to the Internet, you must translate host IPs on that network to a registered IP address that is routable over the Internet. In order to use traditional NAT in this scenario, you would need to purchase a registered IP address for each host on your internal network. Alternatively, you could use PAT to translate all the IP addresses on the internal network to a single, shared IP address that connects to the Internet. PAT, which is also known as NAT overloading, uses 16-bit source port numbers to map and track traffic between an internal host and the Internet.
As you can see, the first letter in each acronym denotes the difference between NAT (Network Address Translation) and PAT (Port Address Translation), which should make it easier for you to remember which does what. Just remember that both NAT and PAT use at least one IP address and that PAT is also referred to as NAT overloading because it uses one IP address for all clients to multiple ports, whereas standard NAT uses a one-to-one IP address relationship per client.