FTP File Transfer Protocol Secured FTP
Â
FTP
File Transfer Protocol (FTP) is a standard network protocol used to transfer files from one host or to another host over a TCP-based network, such as the Internet.
FTP is built on a client-server architecture and uses separate control and data connections between the client and the server. FTP users may authenticate themselves using a clear-text sign-in protocol, normally in the form of a username and password, but can connect anonymously if the server is configured to allow it. For secure transmission that hides (encrypts) the username and password, and encrypts the content, FTP is often secured with SSL/TLS ("FTPS"). SSH File Transfer Protocol ("SFTP") is sometimes also used instead.
Protocol overview
The protocol was first specified June 1980 and updated in RFC 959, which is summarized here.
The server responds over the control connection with three-digit status codes in ASCII with an optional text message. For example "200" (or "200 OK") means that the last command was successful. The numbers represent the code for the response and the optional text represents a human-readable explanation or request (e.g.
Illustration of starting a passive connection using port 21
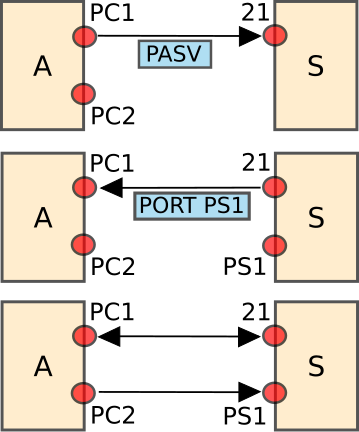
FTP may run in active or passive mode, which determines how the data connection is established. In active mode, the client creates a TCP control connection to the server and sends the server the client's IP address and an arbitrary client port number, and then waits until the server initiates the data connection over TCP to that client IP address and client port number. In situations where the client is behind a firewall and unable to accept incoming TCP connections, passive mode may be used. In this mode, the client uses the control connection to send a PASV command to the server and then receives a server IP address and server port number from the server, which the client then uses to open a data connection from an arbitrary client port to the server IP address and server port number received. Both modes were updated in September 1998 to support IPv6. Further changes were introduced to the passive mode at that time, updating it to extended passive mode.
While transferring data over the network, four data representations can be used:
- ASCII mode: used for text. Data is converted, if needed, from the sending host's character representation to "8-bit ASCII" before transmission, and (again, if necessary) to the receiving host's character representation. As a consequence, this mode is inappropriate for files that contain data other than plain text.
- Image mode (commonly called Binary mode): the sending machine sends each file byte for byte, and the recipient stores the bytestream as it receives it. (Image mode support has been recommended for all implementations of FTP).
- EBCDIC mode: use for plain text between hosts using the EBCDIC character set. This mode is otherwise like ASCII mode.
- Local mode: Allows two computers with identical setups to send data in a proprietary format without the need to convert it to ASCII
For text files, different format control and record structure options are provided. These features were designed to facilitate files containing Telnet or ASA
Data transfer can be done in any of three modes:
- Stream mode: Data is sent as a continuous stream, relieving FTP from doing any processing. Rather, all processing is left up to TCP. No End-of-file indicator is needed, unless the data is divided into records.
- Block mode: FTP breaks the data into several blocks (block header, byte count, and data field) and then passes it on to TCP.
- Compressed mode: Data is compressed using a single algorithm (usually run-length encoding).
Login
FTP login utilizes a normal usernames and password scheme for granting access. The username is sent to the server using the USER command, and the password is sent using the PASS command. If the information provided by the client is accepted by the server, the server will send a greeting to the client and the session will commence. If the server supports it, users may log in without providing login credentials, but the server may authorize only limited access for such sessions.
Anonymous FTP
A host that provides an FTP service may provide anonymous FTP access. Users typically log into the service with an 'anonymous' (lower-case and case-sensitive in some FTP servers) account when prompted for user name. Although users are commonly asked to send their email address in lieu of a password, no verification is actually performed on the supplied data. Many FTP hosts whose purpose is to provide software updates will provide anonymous logins
SFTP
The SSH File Transfer Protocol (also Secret File Transfer Protocol, Secure FTP, or SFTP) is a network protocol that provides file access, file transfer, and file management functionalities over any reliable data stream. It was designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to provide secure file transfer capability, but is also intended to be usable with other protocols. The IETF of the Internet Draft states that even though this protocol is described in the context of the SSH-2 protocol, it could be used in a number of different applications, such as secure file transfer over Transport Layer Security (TLS) and transfer of management information in VPN applications.
This protocol assumes that it is run over a secure channel, such as SSH, that the server has already authenticated the client, and that the identity of the client user is available to the protocol.
SFTP client
The term SFTP can also refer to Secure file transfer program, a command-line program that implements the client part of this protocol, such as that supplied with OpenSSH.
Some implementations of the scp program actually use the SFTP protocol to perform file transfers; however, some such implementations are still able to fallback to the SCP protocol if the server does not provide SFTP service.
SFTP server
There are numerous SFTP server implementations both for UNIX, Windows and z/OS. The most widely known is perhaps OpenSSH, but there are also proprietary implementations. Typically the port used is 22. SFTP file transfer protocol is part of SSH protocol suite.
SFTP proxy
It is difficult to control SFTP transfers on security devices at the network perimeter. There are standard tools for logging FTP transactions, like TIS fwtk or SUSE FTP proxy, but SFTP is encrypted, rendering traditional proxies ineffective for controlling SFTP traffic.
There are some tools that implement man-in-the-middle for SSH which also feature SFTP control. Examples of these tools include Shell Control Box from Balabit and FileGate SFP from Presaris. These provide functions such as SFTP transaction logging and logging of the actual data transmitted on the wire.

