Certify and Increase Opportunity.
Be
Govt. Certified E-Commerce Professional
Session Hijacking
Session
A session refers to temporary information interchange between two devices like logging into a web based email from Google, is actually participating in a session of data transfer between the Google’s server and end user for working on the e-mail account. Session is created and destroyed as per need and fulfillment as in web based e-mail, logging into and logging out refers to it.
Two devices have to negotiate common communication parameters for communicating on a network which is accomplished by a three-way handshake process in TCP/IP based networks. Devices utilize a session token or a sequence number amongst them.
Session Hijacking
Session hijacking is taking over an active TCP /IP communication session without either user’s permission or knowledge. When implemented successfully, attackers assume the identity of the compromised user, enjoying the same access to resources as the compromised user.
Session hijack attacks are usually waged against users that are members of large networks containing a number of open sessions. Network protocols like FTP, Telnet, and rlogin are attractive for such attacks to the attacker, because of the session oriented nature of their connections and they do not implement any security during logon, authentication, or data transmission.
Session Hijacking Types
- Active Session Hijacking – It involves hijacking a already authenticated session as original user has logged in his account or profile and then attacker steal the cookies to hijack the active session and then disconnect the original user from the server. It is done by stealing the original users cookies by using client side scripts by involving social engineering tactics which includes emails, private messaging on forums and on other social networking websites.
- Passive Session Hijacking – In it attackers does not hijack active session instead they capture the login credentials while the original user is trying to establish a new connection with the server, and attacker is sitting silently on the same network and recording the login credentials.
TCP Session Hijacking
It is oldest type of session hijacking. TCP session hijacking actually deals with the successful prediction of the Initial sequence numbers that gets exchanged between two host or a client and the server. Sequence Numbers are exchanged during TCP Three way handshaking.
- Host A sends a SYN bit set packet to Host B to create a new connection.
- Host B will reply with SYN/ACK bits set packet to Host A with a initial sequence number.
- Host A will reply with ACK bit set packet to Host B with Initial Sequence Number + 1
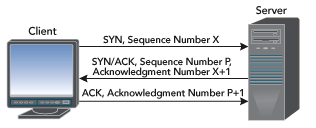
So, if attackers manage to predict the initial sequence number then they can actually send the last ACK data packet to the server, spoofing as original Host then, they can hijack the TCP Connection.
Prevention
Measures to be used to prevent session hijacking include
- Regenerate the session id after a successful login.
- Encryption of the data traffic passed between the connected devices.
- Using a long random number or string as the session key which will take long to guess.
Apply for E-commerce Certification Now!!
https://www.vskills.in/certification/web-development/certificate-in-e-commerce

