Social engineering is the act of obtaining or attempting to obtain otherwise secure data by conning an individual into revealing secure information. It is successful because its victims innately want to trust other people and are naturally helpful. The victims of social engineering are tricked into releasing information that they do not realize will be used to attack a computer network. For example, an employee in an enterprise may be tricked into revealing an employee identification number to someone who is pretending to be someone he trusts or representing someone he trusts. While that employee number may not seem valuable to the employee, which makes it easier for him to reveal the information in the first place, the social engineer can use that employee number in conjunction with other information that has been gathered to get closer to finding a way into the enterprise network.
Criminals use social engineering tactics because it is usually easier to exploit natural inclination to trust than it is to discover ways to hack your software. For example, it is much easier to fool someone into giving you their password than it is for you to try hacking their password (unless the password is really weak).
Security is all about knowing who and what to trust. Knowing when, and when not to, to take a person at their word; when to trust that the person you are communicating with is indeed the person you think you are communicating with; when to trust that a website is or isn’t legitimate; when to trust that the person on the phone is or isn’t legitimate; when providing your information is or isn’t a good idea.
Social engineering attacks typically originate from one of three zones i.e. internal, trusted and external.
- Internal threats come from employees who manipulate other employees to gather sensitive information and access to IT systems. These offenders can include disgruntled employees, temporary employees, employees with criminal tendencies, and ancillary workers such as housekeeping and maintenance staff. Enterprises grant a certain amount of trust to all of these individuals, which can make it easier for them to execute attacks.
- Trusted threats come from other individuals who are formally associated with your organization on a regular basis but are not on your payroll. These can include contractors and consultants, as well as partner organizations. Often, these individuals have a very high level of trust, and thus have access to sensitive data and systems. Yet such potential risks are rarely incorporated into security plans.
- External threats come from people who are not associated with your organization. This category can include recreational hackers, competitors wanting to uncover confidential information, or criminals wanting to steal something. These people have no established trust with your organization, so they look to create short-term trust by using various social engineering techniques.
Some examples of these techniques are:
- Playing the role of an authority, such as an IT administrator.
- Playing the role of an end user.
- Playing the role of someone from a partner organization.
- Playing the role of a telecom technician or another individual who would have physical access to the company’s data systems.
- Tricking an employee into planting malicious software on internal systems.
- Stealing the identity of someone with inside access to IT systems.
Individuals who use social engineering techniques usually follow a common pattern of activity that called the Social Engineering Attack Cycle, which is
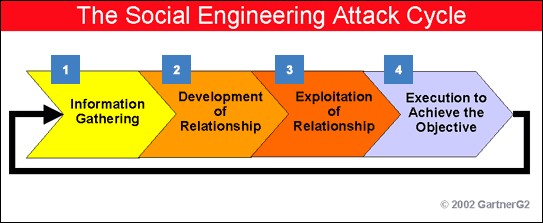
In the first phase, information gathering, an attacker uses various techniques to track down detailed information that can be used to gain the trust of an individual connected to the targeted organization. The attacker will then use this information to develop a relationship with the individual in phase 2 of the attack cycle. This can take one phone call or it can happen over a period of weeks or even months.
After the relationship is established, the attacker will exploit the relationship (phase 3) to get the target to reveal information or perform an action that would not otherwise take place. Phase 3 either accomplishes the attacker’s objective or opens the door to achieving the final objective in phase 4.
Social Engineering Attack Types
All social engineering techniques are based on specific attributes of human decision-making known as cognitive biases. These biases, sometimes called “bugs in the human hardware”, are exploited in various combinations to create attack techniques, some of which are listed. The attacks used in social engineering can be used to steal employees’ confidential information. The most common type of social engineering happens over the phone. Other examples of social engineering attacks are criminals posing as exterminators, fire marshals and technicians to go unnoticed as they steal company secrets.
One example of social engineering is an individual who walks into a building and posts an official-looking announcement to the company bulletin that says the number for the help desk has changed. So, when employees call for help the individual asks them for their passwords and ID’s thereby gaining the ability to access the company’s private information. Social engineering can be broken into two common types of human or computer based.
Human-Based – It refers to person-to-person interaction to retrieve the desired information. An example is calling the help desk and trying to find out a password. It includes
- Impersonation— Te hacker pretends to be an employee or valid user on the system. A hacker can gain physical access by pretending to be a janitor, employee, or contractor.
- Posing as an important user—Te hacker pretends to be a VIP or high-level manager who has the authority to use computer systems or files. Most of the time, low-level employees don’t ask any questions of someone who appears in this position.
- Being a third party—Te hacker pretends to have permission from an authorized person to use the computer system. It works when the authorized person is unavailable for some time.
- Desktop support—Calling tech support for assistance is a classic social-engineering technique. Help desk and technical support personnel are trained to help users, which makes them good prey for social engineering attacks.
- Shoulder surfing—Shoulder surfing is the technique of gathering passwords by watching over a person’s shoulder while they log in to the system. A hacker can watch a valid user log in and then use that password to gain access to the system.
- Dumpster diving—Dumpster diving involves looking in the trash for information written on pieces of paper or computer printouts. The hacker can often find passwords, filenames, or other pieces of confidential information.
- Pretexting, also known in the UK as blagging or bohoing, is the act of creating and using an invented scenario (the pretext) to engage a targeted victim in a manner that increases the chance the victim will divulge information or perform actions that would be unlikely in ordinary circumstances. An elaborate lie, it most often involves some prior research or setup and the use of this information for impersonation (e.g., date of birth, Social Security number, last bill amount) to establish legitimacy in the mind of the target. This technique can be used to fool a business into disclosing customer information as well as by private investigators to obtain telephone records, utility records, banking records and other information directly from company service representatives. The information can then be used to establish even greater legitimacy under tougher questioning with a manager, e.g., to make account changes, get specific balances, etc. Pretexting can also be used to impersonate co-workers, police, bank, tax authorities, clergy, insurance investigators — or any other individual who could have perceived authority or right-to-know in the mind of the targeted victim. The pretexter must simply prepare answers to questions that might be asked by the victim. In some cases, all that is needed is a voice that sounds authoritative, an earnest tone, and an ability to think on one’s feet to create a pretextual scenario.
- Diversion theft, also known as the “Corner Game” or “Round the Corner Game”, originated in the East End of London. In summary, diversion theft is a “con” exercised by professional thieves, normally against a transport or courier company. The objective is to persuade the persons responsible for a legitimate delivery that the consignment is requested elsewhere — hence, “round the corner”.
- Tailgating – An attacker, seeking entry to a restricted area secured by unattended, electronic access control, e.g. by RFID card, simply walks in behind a person who has legitimate access. Following common courtesy, the legitimate person will usually hold the door open for the attacker or the attackers themselves may ask the employee to hold it open for them. The legitimate person may fail to ask for identification for any of several reasons, or may accept an assertion that the attacker has forgotten or lost the appropriate identity token. The attacker may also fake the action of presenting an identity token.
Computer-Based – It refers to having computer software that attempts to retrieve the desired information. An example is sending a user an email and asking them to reenter a password in a web page to confirm it. This social-engineering attack is also known as phishing. It includes
- Phishing is a technique of fraudulently obtaining private information. Typically, the phisher sends an e-mail that appears to come from a legitimate business—a bank, or credit card company—requesting “verification” of information and warning of some dire consequence if it is not provided. The e-mail usually contains a link to a fraudulent web page that seems legitimate—with company logos and content—and has a form requesting everything from a home address to an ATM card’s PIN. Phishing involves false emails, chats, or websites designed to impersonate real systems with the goal of capturing sensitive data.
- Phone phishing (or “vishing”) uses a rogue interactive voice response (IVR) system to recreate a legitimate-sounding copy of a bank or other institution’s IVR system. The victim is prompted (typically via a phishing e-mail) to call in to the “bank” via a (ideally toll free) number provided in order to “verify” information. A typical system will reject log-ins continually, ensuring the victim enters PINs or passwords multiple times, often disclosing several different passwords. More advanced systems transfer the victim to the attacker posing as a customer service agent for further questioning.
- Emails sent by scammers may have attachments that include malicious code inside the attachment. Those attachments can include keyloggers to capture users’ passwords, viruses, Trojans, or worms. Sometimes pop-up windows can also be used in social engineering attacks. Pop-up windows that advertise special offers may tempt users to unintentionally install malicious software.
- Baiting is like the real-world Trojan Horse that uses physical media and relies on the curiosity or greed of the victim. Baiting involves dangling something you want to entice you to take an action the criminal desires. It can be in the form of a music or movie download on a peer-to-peer site or it can be a USB flash drive with a company logo labeled “Executive Salary Summary Q1 2013″ left out in the open for you to find. Then, once the device is used or downloaded, the person or company’s computer is infected with malicious software allowing the criminal to advance into your system.
- URL obfuscation involves, hiding a fake URL in what appear to be a legitimate website address. For example, a website of 204.13.144.2/Citibank may appear to be a legitimate web address for Citibank but in fact is not. URL obfuscation is used in phishing attacks and some online scams to make the scam seem more legitimate. A website address may be seen as an actual financial institution name or logo, but the link leads to a fake website or IP address. When users click the link, they’re redirected to the hacker’s site. Addresses can be obfuscated in malicious links by the use of hexadecimal or decimal notations.
Other types
Common confidence tricksters or fraudsters also could be considered “social engineers” in the wider sense, in that they deliberately deceive and manipulate people, exploiting human weaknesses to obtain personal benefit. They may, for example, use social engineering techniques as part of an IT fraud.
A very recent type of social engineering technique includes spoofing or hacking IDs of people having popular e-mail IDs such as Yahoo!, Gmail, Hotmail, etc. Among the many motivations for deception are:
- Phishing credit-card account numbers and their passwords.
- Cracking private e-mails and chat histories, and manipulating them by using common editing techniques before using them to extort money and creating distrust among individuals.
- Cracking websites of companies or organizations and destroying their reputation.
- Computer virus hoaxes
- Convincing users to run malicious code within the web browser via self-XSS attack to allow access to their web account
Reverse Social Engineering
A reverse social engineering attack is a person-to-person attack in which an attacker convinces the target that he or she has a problem or might have a certain problem in the future and that he, the attacker, is ready to help solve the problem. Reverse social engineering is performed through the following steps:
- An attacker first damages the target’s equipment.
- He next advertises himself as a person of authority, ably skilled in solving that problem.
- In this step, he gains the trust of the target and obtains access to sensitive information.
If this reverse social engineering is performed well enough to convince the target, he often calls the attacker and asks for help.

